- Popular Articles -
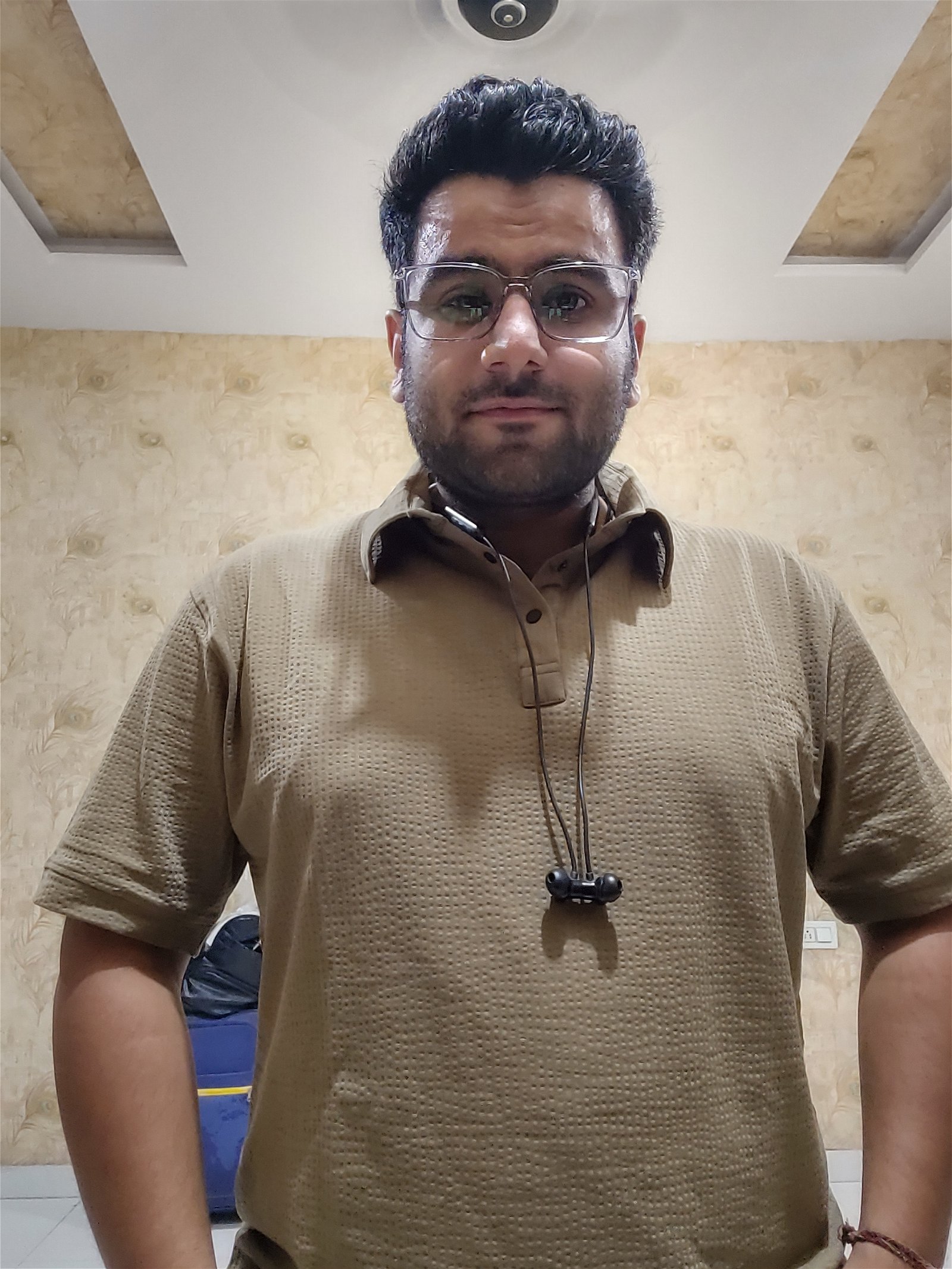
Rating: ★★★★★
Tags: Cyber Security, Malware, Hack, Hacker, USBKill
USBKill is anti-forensic software distributed via GitHub. It is written in Python and is compatible with the BSD, Linux, and OS X operating systems. It is designed to serve as a kill switch if the computer on which it is installed should fall under the control of individuals or entities against the desires of the owner.

Rating: ★★★★★
Tags: Vibe Coding, AI, Artificial Intelligence
Vibe coding is an artificial intelligence-assisted software development technique popularized by Andrej Karpathy in February 2025. The term was listed on the Merriam-Webster website the following month as a slang and trending term.

Rating: ★★★★★
Tags: Blue Hat Hackers, Ethical Hacking
In the ever-evolving world of cybersecurity, the term 'hacker' is often associated with negative connotations, such as illegal activities, malicious intent, and cyberattacks. However, not all hackers fit into this category.

Rating: ★★★★★
Tags: Ethical Hacking, Hacking, Cybersecurity, Cyber Security
In a world that is becoming increasingly digital, security has moved from being a technical concern to a business and national priority. Every organization - whether a startup, multinational company, government department, or hospital relies on digital systems to store data, run operations, and serve users. As cyber threat grow in number and sophestication, the demand for professionals who can protect these systems has skyrocketed. This is where ethical hacking emerges as not just a job, but a highly rewarding career path.

Rating: ★★★★★
Tags: Cryptography, Internet, Security
Have you ever wondered why we need all those HTTPS certificates and why it is so complicated to keep websites secure? It turns out the whole system was kind of flawed from the beginning, and experts are still debating how it should have been built.

Rating: ★★★★★
Tags: Cyber Crime, Cyber Security, Cybersecurity
In today's interconnected world, cybercrime has become one of the most pressing threats to individuals, businesses, and governments. Despite the growing frequency and severity of cyber attacks, many organizations hesitate to report such incidents. This reluctance is often rooted in the fear of reputational damage, particularly among shareholders and clients, and concerns over the exposure of sensitive business data. However, choosing not to report a cyber crime can have far more serious consequences in the long run.

Rating: ★★★★★
Tags: Malware, Cybersecurity, Cyber Security, Key, 2FA
Exploring the limits of two-factor authentication and the importance of user-friendly security design.

Rating: ★★★★☆
Tags: Cybercrimes, Cyber Attack, Cybersecurity
Cyber crimes can be classified based on the origin of the attacker, whether internal or external to the organization facing the cyber attack. Understanding these classifications helps in developing effective cybersecurity strategies.

Rating: ★★★★☆
Tags: Cyber Security, Cybersecurity, Design Principles
As the digital world becomes more interconnected, cyber-physical systems - from smart grids to autonomous vehicles - are increasingly linked with other systems and the broader internet. While this interconnectivity enables greater functionality, efficiency, and innovation, it also introduces a new layer of complexity and risk.

Rating: ★★★☆☆
Tags: Cyber Crimes, Cyber Attack Reasons, Cybersecurity
Cyber crimes have been on the rise, driven by various motivations. These crimes are committed by individuals, groups, or even state actors who exploit digital vulnerabilities for personal, financial, or political gains.



 20
20
 17
17
 14
14