- Popular Articles -
Rating: ★★★★★
Tags: Cyber Security, Cybersecurity, Design Principles
As the digital world becomes more interconnected, cyber-physical systems - from smart grids to autonomous vehicles - are increasingly linked with other systems and the broader internet. While this interconnectivity enables greater functionality, efficiency, and innovation, it also introduces a new layer of complexity and risk.

Rating: ★★★★★
Tags: Low Code, Programming, Scam, Power Apps
Have you observed that organizations are going for low code softwares to automate their processes, but it still takes time like a proper software developer, and sometimes even costs more to implement a low-quality low-code project? Well, you are not alone. I have seen it happening many times, and today we are going to discuss why low-code platforms are basically a scam.

Rating: ★★★★★
Tags: Microsoft Outage, Security Update, Cyber Security
A flawed software update from a cybersecurity company led to a massive Global Tech Outage, disrupting numerous industries and services.

Rating: ★★★★★
Tags: Cybersecurity, Cyber Security, Principles
Designing secure systems in today's complex technological landscape requires more than just basic security rules. The National Institute of Standards and Technology (NIST) offers a modern set of principles that build upon the foundational work of Saltzer and Schroeder, while addressing the challenges of contemporary systems.

Rating: ★★★★★
Tags: Cyber Security, Cybersecurity, System Design, Computer Security
When it comes to building securesystems, especially ones used in important places like the government or military, certain rules or principles help guide the process. Back in 1975, two researchers Saltzer and Schroeder created a set of these security design principles.

Rating: ★★★★★
Tags: Cyber Security, Internet Security
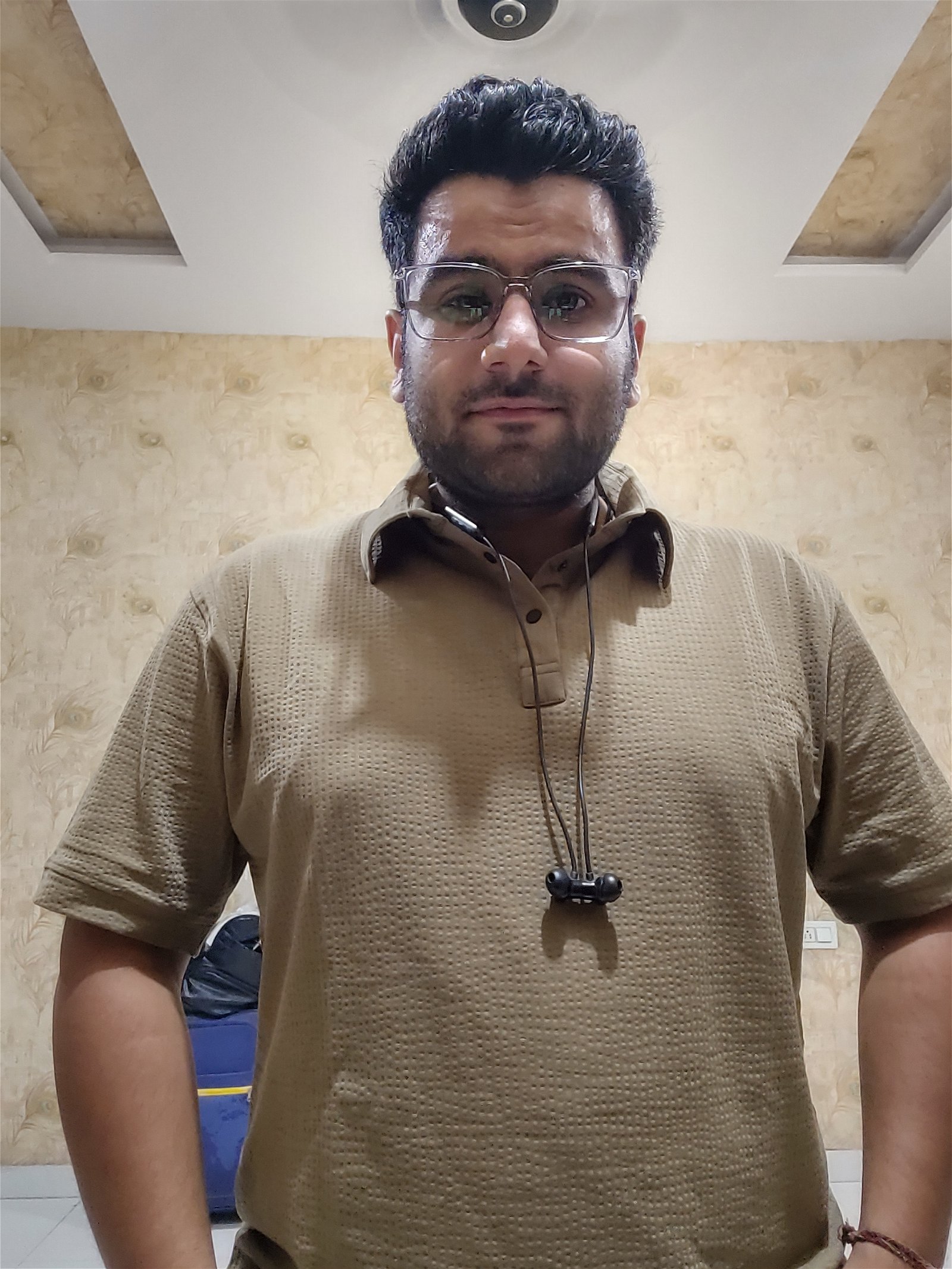
When we talk about cybersecurity, most of the conversation revolves around software vulnerabilities, data breaches, and hackers. But there is one risk very few people think about - what happens when a large group of top security experts are all in the same place at the same time?

Rating: ★★★★★
Tags: Website, Black Hat, Pirate, TPB
The Pirate Bay, commonly abbreviated as TPB, is a freely searchable online index of movies, music, video games, pornography and software. Founded in 2003, by Swedish think tank Piratbyran, The Pirate Bay facilitates the connection among users of the peer-to-peer torrent protocol, which are able to contribute to the site through the addition of magnet links.

Rating: ★★★★★
Tags: Cyber Security, Cybersecurity, System Design Principles
In the modern digital era, data has become one of the most valuable resources - powering everything from social media and smart cities to personalized healthcare and targeted marketing. This transformation is often referred to as the participatory data economy, where individuals not only consume digital services but also actively contribute to the data that fuels them.

Rating: ★★★★★
Tags: Hacking, Cyber Security
In today's digital age, where cyber threats are constantly evolving, robust cybersecurity measures are paramount. Ethical Hacking, often referred to as penetration testing or White Hat Hacking, plays a critical role in proactively identifying and addressing vulnerabilities in computer systems and networks.

Rating: ★★★★★
Tags: MiTM, Spoofing, DNS hijacking
In today’s digital world, protecting yourself online can feel confusing. Terms like Man-in-the-Middle attacks (often called MiTM), DNS hijacking, or spoofing get thrown around – but what do they really mean? And what should you actually worry about?



 20
20
 17
17
 14
14